Living in a Digital World
Worlds within worlds. What do we mean when we talk of a digital world? More correctly we should be talking about what has happened to the world as we knew it before the introduction of information and communication technology (ICT).
What is information and communication technology
ICT includes all technology and services based on technology including computer networks, the internet, the world-wide-web, computers, smartphones, modern switchboards, video conferencing systems, computer applications. Storage disks, memory sticks, and even modern television etc.
Today, ICT is called digital technology. This is because all information captured, stored and transferred using ICT is converted into a digital representation. What that means is we use two states, or two conditions to represent information. This is also called binary representation, where a signal or state is either on or off.
In short, ICT today takes what we do and it converts it into digital formats that enable information to be captured, stored, moved, copied and shared easily. ICT developments have as a result made it possible to deal more efficiently and accurately with more and more information. This has made a positive impact in many scenarios, but as with all change, risks and negative consequences have been introduced.
We are all online as digital citizens
Whether you are consciously working online or not, you are online and you exist in a digital world.
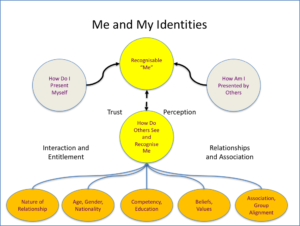
Your records are saved in government and private sector systems. Information relating to your family, your birth records, marital records, bank accounts, education records, travel, immigration property ownership, social activity records, voting records, medical records, and social service entitlement etc. are all online. This information is analysed, interpreted, and shared using computers, databases, networks and applications by various parties.
Even if you are not actively using computers you are a digital citizen. What we say and do using these services is a reflection of our habits and preferences. How we represent ourselves is a portrayal of our online or digital identity.We are now all active in a digital world. We have no choice.
Wherever we go, we complete attendance or visitor registers, have our photographs taken and personal information recorded. Surveillance cameras record our movements. Our signatures, identity documents, drivers licences, access cards, store cards, loyalty cards and bank cards are constantly being digitally scanned.
Government agencies, as well as the companies we buy from, or work for, use digital systems, digital services and networks. Our information and activities are captured, stored and shared on digital systems, and our information moves about over digital networks.
Sometimes we have knowledge of our information being captured and recorded, sometimes we do not. Some example scenarios are discussed below.
Using bank cards at ATMs and merchants
As an example: You may not own a smartphone, or a computer. You may not use Internet cafes or other people’s computers. But you do have a bank account and the bank has given you a bank card. You go to ATMs to deposit and draw cash and you buy from shops or merchants using your card.
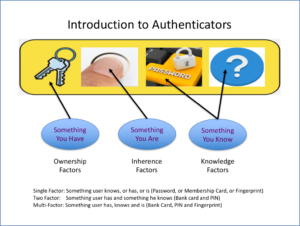
When you use your card at an ATM, the ATM reads the information on your card, combines that information and checks your PIN that was requested, and then authorises you to continue. The ATM is a computer. The information you type is in recorded, transferred over networks to other computers and via a number of network devices so that the bank can authorise your transaction and keep record of what you do. Your information and activity is digital even though you just pushed in a card and entered some numbers on a keypad.
Instant messaging and social networks
WhatsApp has changed the world of instant messaging. Every message we receive and send is captured on a phone (or computer), transferred to WhatsApp’s computers over networks, and sent to the person the message was intended for. WhatsApp, and other know when you are available, when last you were available, which of your contacts are available and saves all your chats before delivering them.
Without thinking about it, we use social media services that add a lot of value in terms of how we communicate and interact. Everything we do using these services is captured and remembered, analysed and acted upon.
Utility applications on Smartphones
Our smartphones provide us with great utility. We take photographs without the need for a real camera, and we use application to find information, and even give us direction to find places.
Consider first the camera. Every time a modern camera takes a picture, it records additional information about the photo. What camera settings were used, and even where and when the picture was taken are recorded. When a photo is saved or shared this information goes with it. Others who access these photos, whether as Facebook, Instagram or WhatsApp posts, attachments in emails, or using any other computer or smartphone application can know where you have been and when. Your activities are online. Add to this the fact that facial recognition can identify you in pictures taking by others, you are not in control of this.
Consider map applications. Map applications must know where you are when helping you navigate. Obviously your position is known and used to indicate best routes to follow and to help avoid traffic congestion. How do these apps know what the traffic congestion is. All users of the app are contributing, perhaps without knowing, where they are, what speed they may be travelling, and this information is used to assist in presenting status of traffic flows. The history of where you are, and where you have been, are recorded, stored, analysed and acted upon.
Consider applications that personalise your experience by remembering what you like and do to give you a better user experience. All these application use techniques to make it easy for you to login, go where you normally go, show you who you last called or messaged, sort your information the way you like etc. This is done by keeping track of your habits and choices and learning more and more about you.
Working at internet cafes
Consider strolling into an Internet Café and using one of their computers. You browse the internet using a web browser on the system. You go to sites, look for information, check your email, go to social media etc.
When you walk out, the system you were working out knows where you have been, what sites you have visited. You have left a trail of breadcrumbs that is on record. Even though the computer was not yours, you are identified by the actions you took.
Whatever applications exist on the systems at the internet café they are at liberty to monitor and record what they choose.
Using another person’s computer
If worried about internet cafes, perhaps you choose to use a friend’s computer. You run similar risks unless you are assured there are no viruses or malicious software agents, key loggers etc. on the system and you understand how to navigate the internet securely.
Benefits of being a Digital Citizen
There are many benefits of being a digital citizen, some of these include:
- Banks can better serve us by placing ATMs in convenient locations for our use. We simply walk up and present our identity, a bank card.
- We use instant messaging, email and social media services to enhance the relationships we have with those we care about, by sharing messages, photographs and videos.
- We can find out anything we need to know instantly by searching on the internet for information and even videos.
- We can store and manage all our personal information and important records online and not worry about the risks of loss or theft of a computer or mobile device.
- We can use online services to manage our personal and business lives.
- Companies we buy from from and government agencies can provide us with better service, even personalised service by doing so online.
Risks of being a Digital Citizen
There are some risks of being a digital citizen, some of these include:
- We can be targeted and flooded by digital communication and advertising as our digital identities becomes widely known.
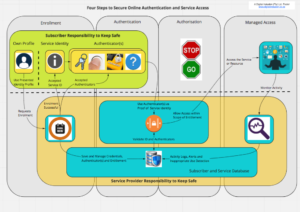
- Personal and confidential information of ours and about us is stored online. Access to this information is protected through the use of a Digital Identity that represents us. It is possible that this information ends up in the wrong hands and exposes us to risks if not adequately secured.
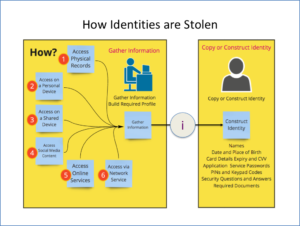
- We have personal access to services online. People can steal our digital identities, pretend to be us and gain access to our personal services, or get access to new services using our identities.
- People using our identities may conduct activities that damage our real-worlds and digital world reputations.
Choices in a Digital World
We choose to use services.. By doing so, we expose ourselves to risk. The benefits of the service may, in our view, outweigh the risks. We make a call to trust the service providers, the systems, and the networks we use to gain access to the services.
We have some control regarding security, we need to understand what is in our control and what is not in our control.