Information risk Prevention
There are a number of ways you can mitigate or minimise the risks of information exposure.
What should I share
Perhaps the best place to start is to think about what you should and should not be sharing. If you have given this enough thought, you will be more aware of the risks you face when going about your everyday online activities.
Who should I share information with
Consider who you should share information with. You have different ‘disclosure boundaries’ depending on who you are interacting with. You will share different information with your wife, your boss, the shopkeeper, and strangers you engage with when commuting.
Have a clear picture of what you are prepared to share in each of the scenarios and online environments you are engaging in.
Managing Location Tracking
On your devices, PC and mobile, take charge of the exposure of your location information. Only enable location tracking for applications that you trust, and applications that are location dependent (maps while navigating). Why allow application tracking for general applications (web-browsers, social media services, your camera etc.)
A photograph that you share on WhatsApp or Facebook will contain information about where you were, on which day and at what time the picture was taken unless you disable location tracking on your camera devices (smartphone etc.) With facial recognition services being integrated into online service applications, you may not even be aware that the people in your photographs are now able to be recognised and tracked, and you are responsible for having enabled this.
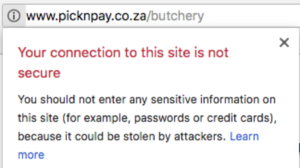
Sharing Financial Information
No banking services should ever ask you to share for you banking details online or over the phone. Your password, and PINs should only ever be known by you. Emails and phone calls that ask for this information are likely to be from other parties, and not the bank.
Perhaps consider requests made for this information online as similar to how you would handle such an enquiry if a stranger met you in the street and ask for the information. How do you know who the person requesting the information is, and whether it makes sense to give them the information? As a general guide, do not share information unless you initiated the conversation and you have assured yourself the person you are dealing with is the right person to engage with.
If anything looks suspicious, ignore it, delete it, do not respond or enter into discussions or interactions. If any financial institution really wants to get hold of you, they have your details. Your job is to ensure your records are up to date. You are in control of your authenticators (passwords and PINs, email address, phone number etc. Keep your profiles up to date yourself.)
Guidelines for risk management
Managing online profiles
If any online service provider really wants to get hold of you, they have your details. Your details are in your profiles. Your job is to ensure your records are up to date. You are in control of your online profiles and authenticators (passwords and PINs, email address, phone number etc.). Keep your profiles up to date yourself.
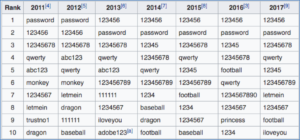
Make sure you have a good password and PIN strategy. See the section on Password risk Management.
Identifying ‘phishing’ and malicious activities
We receive high volumes of emails and messages. Inherently we would like to trust everyone who contacts us and engages with us. Unfortunately, the digital world has enabled access to us by those we do not know and are often unable to verify their identities.
Look out for emails and messages that are suspicious. If information is being requested from you, be alert and ask if this is a normal request that can fairly be expected. If you have not initiated the conversation, and it comes as a surprise, be very cautious.
Phishing emails look authentic. The email name address appears to be ok, but if you check closely the underlying email address will likely look odd, or have one or characters that do not match the institution represented. In many cases the person with malicious intent has even copied images, screen layouts, web page layouts etc. that are nearly identical to the organisation they are claiming to representing.
If anything looks suspicious, ignore it, delete it, do not respond or enter into discussions or interactions. If any online service provider really wants to get hold of you, they have your details. Your job is to ensure your records are up to date. You are in control of your authenticators (passwords and PINs, email address, phone number etc. Keep your profiles up to date yourself.)