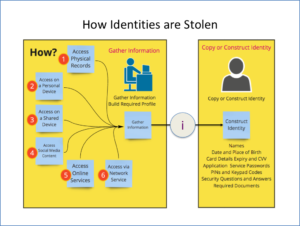
DIM-03-02 How Identities are Stolen
Profile Building
Information that may on its own not appear to be information that is valuable, when combined with other information can be used to build a personal profile. Knowing a person’s profile can help answer security questions, and facilitate someone acting as that person.
Where information is kept determines how it can be accessed. Different strategies may be followed to gain access to information that can assist in profile building and ultimately identity theft. Information is distributed. Some information is kept as a physical record, some as an online record and some as both.
Physical records
You probably have a number of physical documents that you perhaps keep at home. These could include:
- Identity documents, Driver’s Licence, Passport
- Bank cards
- Social benefit cards
- Educational qualifications
- Bank statements
- Account statements (retailers and utilities)
- Medical records
- Insurance Records
- Contracts
Some of these records must be kept, others not. How do you protect them from damage or theft? How do you dispose of documents when you no longer need to keep them?
Information can be physically stolen by intercepting delivery, theft from your home, office, bag or vehicle, and even from waste disposal.
Information can be electronically stolen by using mobile phone cameras to capture documents that are left accessible. By photographing for example the two sides of your bank card, a person can use this information to shop online at your expense.
Focus in later sections will cover Bank Card usage, risks etc.
Personal devices
Personal devices include any mobile phones, tablets, laptops and computers that you use. These devices have your information on them. Do you secure the devices effectively?
Theft of a device may result in access to all your information on that device. If someone gets access to your device, can they access all your services?
Information can also be stolen from your device without stealing the device. When working on public networks or using Bluetooth services your device may be vulnerable to access by others.
Shared devices
Using devices that belong to others introduce some additional risks. Computers and other devices that belong to a friend or colleague, are located in computer lab, library or internet café are not under your control. When working on these devices you leave a trail of information that can be accessed by others. Are you diligently ensuring that no information trails are left behind, no services left logged in to?
Social media content
Social media services encourage us to share information freely. Tools allow you to easily share what you do, where you go, what you saw, who you were with, what you believe and what you care about. This information generally ends up in the public domain for all to see and do with what they please.
You are being followed by others and are encouraged to believe this is a good thing. Do you know who is following you? Do you know who all the members of your groups are?
Over time, you build up and share a profile of yourself for all to see. This assists those who wish to target you and steal your identity.
Online service content
Online storage is as good as free. Why invest in your own storage on your own systems when you can have it all online and get to it from anywhere, anytime? So can others if you are negligent. Are you sharing your online content with others, and if so is it being done securely? Plenty of services offer shared storage areas for collaborating in business or within social circles.
Network access to content
Mobile network service providers charge for data. Wi-Fi hotspots enable us to use data at no charge. What price are we paying? Public networks, may expose us to eavesdropping, where people we do not know intercept our communication and perhaps gain access to our devices while we use public networks to access services on the internet.
Bluetooth services allow you to share content with our friends. Are you controlling access to your mobile device effectively?