DIM-02-01 Identity Management Introduction
Who are we?
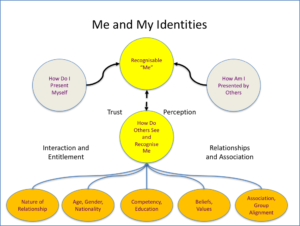
How do we identify ourselves? How do we present ourselves to others? How do others recognise us, and identify us? Do you have multiple forms of identity?
Why do we have an identity?
We need to be known, and identifiable, if we are to benefit from accessing services. Service providers, in both the real world and the online world, need to ensure that services we are entitled to are not given to others. Our identity, and the ability to prove our identity is the key to gaining access to services.
How are identities used?
In principle, we gain access to services and information based on our our identities. This involves a four step process:
- Presentation of our identity – We present our identities when wanting to gain access to services or information
- Authentication of our identity – The service provides checks our identities against know records to see if they are authentic (valid) and they are comfortable that we are who we claim to be.
- Authorisation of our right to access – Once satisfied with the authenticity of our identity, the service provider authorises our access.
- Access to services and information – We are now free to access the services and information we wanted.
Real, physical world identities
As citizens, we should have been registered at birth. Our government opens and maintain a record for each individual, and each individual is given an identity. This is managed and regulated by a specific government department (Home Affairs in South Africa). Proof of your identity could be through the presentation of:
- Birth Certificate – Proof of the individual’s registration as a citizen.
- Identity document or card – official document with personal information and photograph. Issued to citizens.
- Passport – official document with personal information and photograph. Used to allow individual to travel internationally.
- Driver licence – linked to identity record, with a photograph. Official document detailing individuals right to drive and operate certain types of vehicles.
Outside of official government issued identity related documents, alternative documents or tokens can be presented to gain access to specific services and resources:
- Membership Card – Club, society or professional association identity with name, membership number etc. Entitles the member to use club or society services and resources.
- Student Card – Education institution association with name, student number, photograph etc. Enables student to gain entry to facilities and access institutional and other campus services and resources.
All of the above forms of identity proof, are physical and normally presented by the individual on demand. The person or system that authenticates the identity can visually compare photographs, signatures etc., and can make a call to authorise access to services or resources for the individual.
Online, digital identities
In the online world, we use digital identities. Each service we wish to access and use online has their own requirements for identifying and authenticating users. Users choose to subscribe to services and engage with the service provider to establish an acceptable form of identification and a means to verify that the individual who uses that identity online is in fact the person who they claim to be.
Examples of services and identities include:
- Username and password to gain access to a device
- Username and password to gain access to an online application service
- Username and a personal identification number (Fixed PIN or one-time pin OTP)
- Bank card number and PIN – normally processed digitally to scan the card and then challenge the presenter to enter something known only to themselves (a Personal Identification Number or PIN). Having the card physically and knowing the information requested is taken as implied proof of identity. If processed manually, additionally information may be asked for.
So, if you use email, Facebook, WhatsApp, Dropbox, and perhaps Google services, you already have multiple identities online. Some identities may be linked to a known mobile phone number, others to a username that you or a service provider chose. Each service may have its own password or alternative approach to verifying you are who you claim to be. Anyone who pass the authentication test is assumed to be you.
Setting up an Identity
- Register with a service provider to be entitled to benefit from their services. Setup a unique identity as required by the service provider.
- Once registered, present proof of your unique identity to be authorised to gain access to services.
Our National Identity
There are a l lot of people on this planet. Each of us presents ourselves to the world and establishes relationships with others. We become known. Our name, given or registered, may identity us within a known circle. But our name may not be unique. Wherever we associated in a business, community, club, educational institution, or professional association, we need to be able to prove our identity to be authorised to gain access to the benefits of our association.
- As a citizen of a country we have certain rights (and responsibilities). Our rights may includes access to basic services, healthcare, schooling, social benefits, and the right to vote etc. Our responsibilities may include contributing back to society in the form of paying taxes, military service etc.
- In order to secure access to our rights as a citizen, we are registered, typically at birth, given a unique identifier (identity number) and our name, parents information etc., are recorded in the national population register. Our unique identity is used by all government services as the index for information related to us. This can includes voting records, birth and death certification, criminal records, health records, tax records, etc. To prove we are who we are, we are issued with a proof of identity document or card by our national home affairs department.
Physical World Identities
As discussed above we need to prove our identity in the physical world. We may have multiple identities each with their own approach to proving we are who we claim to be. Most forms of identity proof have a photograph, signature and a link to our national identity to allow for validation of identity.
- National Identity Document / Card – Identity document used as proof of citizenship. This is the primary proof of our identity as an individual and may be referenced on all other identity forms.
- Passport – Has own document number but is linked to our national identity. Sometimes a passport may be accepted as proof of identity.
- Driver’s Licence – Evidence of our competency and right to drive a vehicle. Linked to national identity. May sometimes be accepted as proof of identity
- Club or Professional Association Member Card – ensures access to club services. Membership number unique, may be linked to national identity
- Student Cards – Unique student number, may be linked to national identity number.
Digital World Identities
Online, we establish multiple identities. When subscribing to digital services online, we register with the service provider, open an ‘account’ whether commercial or not, and provide information by which we can be recognised. There are two key considerations for setting up an account:
- We must have a service ‘username’ which must be unique as far as the service provider is concerned.
- We must be able to prove we are the right person accessing the service by setting up a secret ‘password’ that must be offered in association with the unique username.
The ‘username’ may be given to us by the service provider, or we may be able to define our own username as long as it is a unique username in the service provider’s records.
Authentication and Authorisation
Essentially each service provider maintains a record of authorised or registered users and a unique method to verify their identity. Each time a user attempts to access their service they must present their credentials, normally a username and secret password which is checked against the service provider’s records. When successful, a user is authorised to use the services and granted access.
If we have an email account as our username, the email address must be unique, and only be used by ourselves. As a result of this, we could use the email address as a username for other systems as well.